Overview
A Circle is a secure virtual private network between a group of devices that is set up by a Circle Owner - through our hybrid P2P authentication process. Within each Circle, there are Secure Capsules (called “Topic” in API methods) that can contain anything you wish.
On the Endpoint Device
Our breakthrough hybrid P2P + Cloud architecture powers a new level of privacy, security and access control for developers
On the Endpoint Device
In the Cloud
Circle Service
Lightweight Thin Client - install & forget
- AES 256 Encryption
- Key Management
- Invite + Authentication
- Circle Secure Capsules

Keys Bound to the Device
- Bound to device keychain / Trusted Platform Module (TPM)
Circle Secure Capsules
AES 256 encrypted containers for anything - files, databases, structure & unstructured data

A Circle can contain any number of Open or Locked capsules

Open:
accessible with the master capsule key

Locked:
separately encrypted with unique key
Circle Web Services
Hybrid P2P
- Data Transport Service Bus
- Messaging
- Data back-up and restore
- Licensing

Circle Server has copies of each private secure capsule – as data blobs. But it has no keys and zero ability to open them or even know what they are or who they belong to (other than knowing which customer has the license to use them).
Encrypted Private Peer Network
Bound to Device TPM
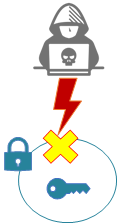
Keys are encrypted and can only be used on the device they were authorized

Everything inside of a Circle and its secure capsules – including the data of the users – is private and encrypted at all times
Bound to Device TPM


Encrypted on the Cloud NO KEYS
Circle Secure Capsules can contain anything
In the use case of credential free authentication, you can store secrets & hashes, certificates – anything helpful to identity verification + authentication

Examples:
- Tokens
- Secrets
- Hashes
- Certificates
- Device / User History &Activity
- Risk Posture
You can also store policies, or even a policies engine and logic that is impervious to external attacks or interference

Examples:
- Policies - executed by external application
- Policies engine – executed internally with Circle
- Policies logic / application
- Keys / other cryptographic means for policies enforcement
Databases, large media files, sensitive ePHI, unstructured data files – you name it!


Even better, the data itself can be kept in the Cloud – and given the user when called like any cloud app

While the keys always remain on the device
Implementation and use case examples
Circle Secure Capsules are incredibly flexible and powerful. We have only scratched the surface of what can be done with them. These are some of the low hanging fruit use cases that we know of and have implemented ourselves in various ways as we developed the platform. We look forward to learning more as we work with our developer community.
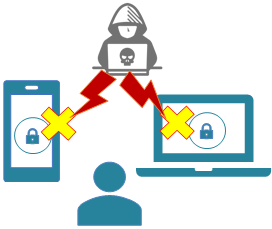
Cryptographic Credential Free Authentication
Circle Access Desktop uses Secure Capsules to store secrets, tokens, or at the highest level, encryption keys for digital signatures. If Circle Access Desktop and Circle Access Mobile are both installed, then they use Secure Capsules and creates a secure connection between the Circle Access Mobile application and Secure Capsules that are installed and managed by Circle Service on devices the user has authorized.
- Learn More about Cryptographic Credential-free Authentication
- Circle Access Product Home
- Circle Access Desktop API Home
- Circle Access Lite
Use Cases:
Unspoofable Human-in-the-Loop Identity Verification
Circle-of-Trust uses Secure Capsules - together with other unique properties of Circles and its patented P2P authentication method - to enable ultra-secure human-in-the-loop identity verification. At the highest levels, this is performed entirely within AES 256 encrypted Circles, with direct out-of-band identity verification between human users - that is cryptographically fused to authentication.
Use Cases:
Distributed, Private and Secure Data Storage and Communications
Circle End-to-End Data Protection and Circle Enterprise Data Visibility & Control both use the properties of Secure Capsules that enable the storage, use and control of data on the client side (endpoint device) by the data owner - which is, in this case: the application / Web server itself. Secure Capsules are also the repositories for data that is exchanged between users in secure communications within Circles.
Use Cases:
Secure Transactions and Digital Trust for User Journeys
Circle Access Digital Trust for User Journey uses the data security and control properties of secure capsules, along with the immutable DLT that is built-in to them, to ensure digital trust for user journeys, actions, interactions and transactions. These are combined into Circle Access to support multi-party authorization workflows.
Use Cases:
End User Data Security and Privacy
Circle Data Privacy and Compliance uses Secure Capsules - together with other unique properties of Circles and its patented P2P authentication method - to enable developer to give end users privacy and control of their data and communications.
Use Cases: